Donald Gainsborough stands at the intersection of high-stakes policy and federal acquisition as a leading voice at Government Curated. With a career dedicated to navigating the labyrinth of legislative mandates and defense requirements, he provides critical oversight on how the government manages its most sensitive assets—its people. In his current capacity, he monitors the evolution of the Defense Counterintelligence and Security Agency and the shifting landscape of the Trusted Workforce 2.0 initiative.
This conversation explores the technical and operational hurdles of transitioning to continuous vetting, the inherent financial risks of small-business set-asides for massive contracts, and the potential for structural constraints to impede national security. Gainsborough also addresses the strategic implications of compressed procurement timelines and provides his outlook on the future of the Case Processing Operations Center.
How does integrating real-time continuous vetting into traditional case processing change the technical requirements for a workforce? What specific operational challenges arise when shifting from periodic reinvestigations to constant monitoring, and how should agencies manage the resulting surge in data alerts?
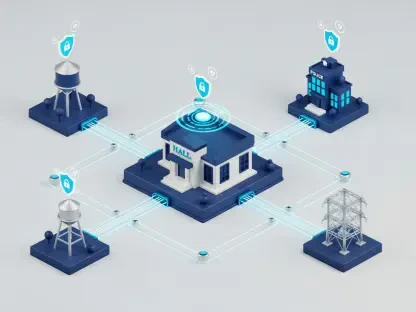
The shift from periodic reinvestigations every few years to a near real-time continuous vetting model is a generational transformation that requires a much more tech-savvy workforce. We are moving away from clerical intake and toward a model that demands high-level analytical services capable of interpreting a constant stream of threat alerts. This creates a massive operational surge; instead of processing a million discrete cases annually, the system must now handle millions of ongoing investigative actions simultaneously. To manage this data deluge, agencies must implement sophisticated automated filtering and technology integration that allows human analysts to focus on high-risk flags rather than drowning in noise. It is no longer just about steady-state processing; it is about building a workforce with the adaptability to pivot as new threat vectors emerge in the data.
When a contract requires managing over 800 full-time employees and millions of annual investigative actions, what financial risks are inherent in a total small-business set-aside? How can a smaller firm practically front capital expenditures while competing with large corporations for top-tier security talent?
Setting aside a contract of this magnitude for small businesses introduces significant financial fragility into a mission-critical operation. A firm winning a contract for 800+ personnel must have the liquid capital to front massive payroll expenses and capital expenditures long before the first government invoice is paid. This creates a “structural constraint” where a small firm might struggle to maintain the management discipline and benefits packages required to lure top-tier security talent away from established large corporations. There is a high risk of the contract becoming a de facto pass-through, where the small business has the name on the door but lacks the deep pockets to handle the volatility of a national security surge. We have to ask if it is fair to the mission—or the small business—to place them in a position where a three-month delay in government funding could collapse the entire vetting enterprise.
New federal directives mandate comprehensive reviews for small business set-asides exceeding $20 million in value. What criteria should be used to determine if a procurement is “structurally constrained,” and what are the specific consequences for national security if these reviews delay the award process?
A procurement is structurally constrained when the sheer scale and complexity of the work—such as the Case Processing Operations Center’s requirements—exceed the realistic capacity of the small business industrial base to perform independently. We should look at whether the award requires specialized systems or a level of financial bonding that effectively limits competition to only a handful of firms that might be over-leveraged. The consequences of getting this wrong are severe; if these mandatory reviews under the latest January 16 memorandum are conducted poorly or too late, they trigger litigation and massive delays. In a world where the U.S. is in constant conflict, any pause in processing background investigations directly hinders our ability to put cleared personnel into the field, effectively stalling national readiness.
Agencies sometimes release requests for information with response windows lasting only a few days. How does this compressed timeline impact the quality of industry feedback, and what steps can be taken to ensure that incumbents do not gain an unfair advantage during such rapid procurement cycles?
When you release a draft solicitation with only a few days for response, you are essentially signaling that you aren’t looking for new ideas, but rather confirming what you already know. These compressed timelines severely undermine the quality of industry feedback because only the incumbent, who already understands the nuances of the 800-person workload, can provide a detailed response that quickly. To level the playing field, agencies must provide at least two to three weeks for meaningful industry engagement, allowing non-incumbents to perform the due diligence necessary to offer innovative solutions. If we continue with “business as usual” short-suspense requests, we are stifling the very competition that the small business program is supposed to encourage, leading to a stagnant and less resilient supply chain.
Delays in background investigation processing can ripple across the entire federal hiring enterprise. What metrics should be prioritized to ensure system resilience during a contract transition, and how can the government balance socioeconomic goals with the need for immediate, large-scale surge capacity?
During a transition of this scale, the government must prioritize “time-to-hire” metrics and investigative action completion rates above all else to ensure the hiring pipeline doesn’t freeze. We need to see a clear plan for “surge capacity”—the ability to scale up staffing or technical processing power instantly if the threat landscape shifts or a backlog begins to form. Balancing socioeconomic goals is important, but it should not come at the expense of a single point of failure; perhaps a better approach is a tiered strategy that involves small businesses in meaningful sub-roles rather than a single, consolidated small business award. This ensures we meet our diversity targets while maintaining the “big-engine” infrastructure and financial backing that only a full and open competition can reliably provide.
What is your forecast for the future of the Case Processing Operations Center?
The CPOC will eventually have to move away from being a monolithic, consolidated contract and instead become a more modular, technology-driven ecosystem. As Trusted Workforce 2.0 matures, I expect the center to shift 70% of its workload toward automated continuous vetting, reducing the reliance on manual clerical tasks while increasing the demand for specialized cyber-analysts. However, if the current acquisition strategy remains rigid, we will likely see a cycle of protests and performance issues that will eventually force the government to reopen the requirements to a broader pool of large-scale integrators. The future of vetting is fast, automated, and global, and our procurement strategies must evolve to match that speed or risk leaving our most sensitive roles unfilled.