The recent digital assault against Kash Patel, a prominent figure in the national security landscape, underscores the increasingly aggressive tactics employed by foreign state-sponsored entities to compromise high-profile American targets. Federal investigators recently confirmed that the Iran-linked hacking collective known as Handala successfully breached the private communications of the former government official. The group released a trove of personal materials, including private photographs, professional resumes, and extensive email correspondence primarily spanning the period from 2012 to 2014. While the data itself is several years old, its public dissemination serves as a calculated psychological operation. This breach is not an isolated event but part of a broader, more persistent campaign orchestrated by actors that the Department of Justice has officially tied to Iran’s Ministry of State Security. By targeting individuals with deep ties to the intelligence community, these adversaries aim to undermine the perceived security of those tasked with protecting the nation.
Persistent Threats and Broader Institutional Vulnerabilities
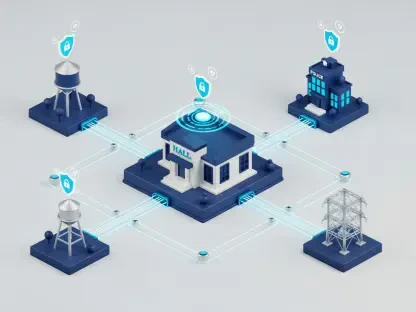
Department of Justice officials have already vouched for the authenticity of the leaked Patel documents, noting that the persistence of Iranian cyber warfare remains undeterred by recent regional military developments. This specific operation by Handala follows a string of high-stakes claims, including a significant intrusion into the systems of the medical manufacturer Stryker and an alleged data theft from the defense contractor Lockheed Martin. Although Lockheed Martin has formally denied any evidence of a system compromise, the sheer scale of these claims highlights the group’s ambition to disrupt both the public and private sectors. This incident coincided with a separate, highly sophisticated breach of a law enforcement surveillance system attributed to Chinese state-sponsored actors. Together, these events represent a multifaceted threat landscape where global adversaries collaborate or compete to exploit digital weaknesses. The intersection of these distinct cyber campaigns suggests that American institutional stability is being tested by multiple fronts simultaneously, requiring a more robust and unified defensive posture across all levels of government.
Strengthening Defensive Protocols Against Evolving Espionage
The breach necessitated a comprehensive reevaluation of how former and current high-ranking officials managed their digital footprints across personal and professional platforms. Stakeholders recognized that even decade-old data remained a potent weapon for extortion or reputational damage when stored on insufficiently secured servers. To mitigate these risks, organizations prioritized the implementation of hardware-based multi-factor authentication and advanced encryption for legacy archives. Federal agencies accelerated the transition to zero-trust architectures, ensuring that access to sensitive information was strictly regulated regardless of the user’s historical credentials. Proactive threat hunting became a standard practice, allowing security teams to identify lateral movement within networks before exfiltration occurred. These defensive adjustments provided a necessary framework for neutralizing the impact of future Iranian or Chinese interference. The situation demonstrated that long-term digital hygiene was as critical as active defense, leading to new protocols for the permanent scrub of non-essential historical data from interconnected systems.