The sudden silence of a digital system within a small-town clerk’s office can be the first sign that an entire community’s essential services have been hijacked by invisible, global extortionists. For years, the prevailing narrative of cyber warfare centered on the dramatic breaches of multinational corporations and high-stakes espionage against federal agencies. However, as the digital landscape evolves, a significant and troubling shift has occurred in the strategic targeting patterns of ransomware syndicates. These criminal organizations have increasingly turned away from the “hardened” perimeters of Fortune 500 companies, opting instead to focus their efforts on the “soft underbelly” of local governance. This migration toward smaller targets is not a matter of chance; it is the result of a deliberate, cold, and mathematical analysis performed by attackers who have realized that a town hall in the heart of the country can be a far more lucrative and less risky victim than a global financial institution.
This new frontier of cybercrime treats local municipalities as the ideal testing ground for sophisticated extortion techniques. While a multi-billion-dollar corporation might employ hundreds of cybersecurity professionals and maintain a state-of-the-art Security Operations Center, a small municipality often relies on a skeletal staff to manage everything from sewage billing to police records. The hackers recognize that these communities are the backbone of daily life, and when their essential services go dark, the pressure to resolve the situation is not just financial—it is deeply personal and political. When residents cannot pay their utility bills, when emergency services lose access to historical data, or when local property records vanish, the outcry from the public creates a “pressure cooker” environment. In this atmosphere, the traditional cost-benefit analysis used by criminals favors the attacker, as the urgency of restoring the basic functions of civilization often leads to a higher probability of ransom payment.
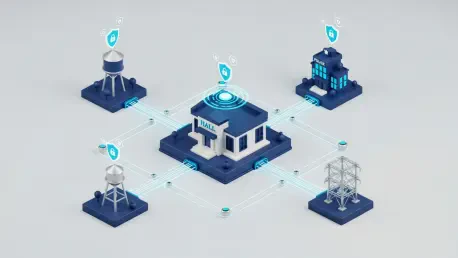
The real-world impact when a small community’s digital infrastructure is paralyzed extends far beyond a simple computer outage; it represents a fundamental breach of the social contract between citizens and their local government. In many instances, a successful ransomware deployment does more than just lock files; it halts the machinery of justice, delays the distribution of social services, and can even threaten public health if water and sanitation controls are integrated into the compromised network. This shift in the crosshairs represents a transition from data theft to functional paralysis. As these attackers move through the digital corridors of local town halls, they are not just looking for credit card numbers—they are looking for the keys to the city, knowing that the more essential the service they disrupt, the more leverage they hold over the local administration.
The New Frontier of Cybercrime: Why Your Local Town Is in the Crosshairs
The traditional image of the high-profile hacker seeking to take down a massive bank or a global tech firm has become an outdated cliché in the modern era of organized digital crime. Today, the most successful cybercriminal enterprises operate like agile startups, constantly seeking the highest possible return on investment with the lowest possible risk of detection or failure. This economic reality has led these groups to the realization that attacking a small municipality is often far more efficient than attempting to breach a high-security corporate network. While a large corporation may have a dedicated team for threat hunting and incident response, a local government often has a single IT professional who is also responsible for maintaining physical hardware and troubleshooting basic software issues for every department. This disparity in defensive resources makes the local town hall a primary target for automated scanning tools that look for the path of least resistance.
The “Cold Mathematical Reality” of these attacks is rooted in the fact that criminals are increasingly using data analytics to select their next victim. They look for organizations that have a high “criticality of service” combined with a low “defensive maturity.” Small municipalities fit this profile perfectly because they are legally and ethically obligated to maintain services that the public cannot live without, yet they rarely have the budget to implement the multi-layered security protocols seen in the private sector. Furthermore, the political nature of local government adds a layer of leverage that does not exist in the corporate world. A CEO may answer to a board of directors, but a city manager or a mayor answers to a frustrated electorate. When the local police department cannot process arrests or the fire department loses access to building blueprints during an emergency, the political cost of delay becomes astronomical, often making a ransom payment seem like the only viable path to restoration.
Beyond the technical aspects of the breach, the human cost in a small community is profound when digital services go dark. In a town of 10,000 people, the government is not a faceless entity; it is the source of clean water, the keeper of the local library, and the administrator of the parks where children play. When a ransomware group freezes the municipal network, they are effectively holding the community’s way of life hostage. The psychological impact of seeing a familiar local institution rendered helpless by an anonymous international criminal is jarring and erodes the public trust. This erosion of trust is often a secondary goal for certain types of attackers who seek to destabilize local governance. As these incidents become more frequent, the realization is setting in that no community is too small to be noticed, and the digital walls that once felt secure are proving to be surprisingly permeable.
Understanding the Vulnerability of Small-Scale Governance
The true scale of the threat becomes apparent when one considers that there are approximately 35,000 local governments currently operating across the United States, each representing a potential entry point for a motivated attacker. This vast landscape of decentralized governance creates a massive “attack surface” that is nearly impossible for federal authorities to protect uniformly. While federal and state governments have significantly increased their cybersecurity budgets, these funds often struggle to trickle down to the smallest jurisdictions where they are needed most. Consequently, a significant portion of these 35,000 entities remains in a state of high risk, operating with legacy systems and outdated security protocols that are no match for the automated exploits used by modern ransomware gangs. The sheer volume of potential targets ensures that even if a criminal group is unsuccessful in one town, they can simply move to the next one with minimal effort.
In this environment, cybersecurity can no longer be viewed as a technical “IT problem” relegated to a basement office; it has emerged as a fundamental pillar of public safety, equivalent to police and fire protection. This shift in perspective is necessary because the consequences of a digital failure are now identical to the consequences of a physical disaster. A city that loses access to its emergency dispatch system or its traffic control network is just as vulnerable as a city facing a natural disaster. Therefore, local leaders must begin to treat digital risk management with the same gravity as they treat infrastructure maintenance and public health. The challenge lies in the fact that unlike a bridge or a road, digital vulnerabilities are often invisible until they are exploited, making it difficult for local officials to justify the necessary expenditures to a public that may not fully grasp the severity of the threat.
Data suggests that ransomware attacks have a disproportionate impact on communities with populations under 50,000. These smaller towns often lack the financial reserves to absorb the massive costs associated with a breach, which include not only the potential ransom but also the astronomical fees for forensic experts, legal counsel, and long-term system restoration. For a large city, a million-dollar recovery effort is a budget line item; for a rural county or a small town, it can lead to a fiscal crisis that necessitates cutting other essential services or raising taxes. This economic vulnerability is a key component of the attackers’ strategy, as they know that the smaller the community, the more likely they are to be overwhelmed by the complexity of the recovery process. The result is a predatory cycle where the most vulnerable jurisdictions are targeted by the most sophisticated criminals, creating a significant gap in the national security posture.
The Strategic Calculation: Why Small Towns Are “Favorite Prey”
The emergence of small municipalities as “favorite prey” for cybercriminals is driven by a stark resource disparity gap that leaves local officials at a significant disadvantage. In many small jurisdictions, the entire technological infrastructure is managed by one or two “IT generalists” who are tasked with an impossible range of responsibilities. These individuals must maintain physical servers, manage complex cloud migrations, provide user support for hundreds of employees, and somehow find the time to monitor the network for signs of a sophisticated intrusion. In contrast, the criminal groups attacking them are highly specialized, often consisting of different teams for initial access, lateral movement, and the final encryption of data. This “asymmetric warfare” means that a single, overworked municipal employee is effectively standing alone against a global network of specialized professionals.
Furthermore, most small-town budgets do not allow for the establishment of dedicated Security Operations Centers (SOCs) that provide 24/7 monitoring and threat detection. Without these continuous monitoring capabilities, an attacker can linger in a municipal network for weeks or even months before the final ransomware payload is delivered. During this time, they can meticulously map the network, identify where the most sensitive data is stored, and—most crucially—locate and compromise the backup systems. The lack of a proactive defense means that by the time the local IT staff realizes there is a problem, the battle has already been lost. The absence of sophisticated defense-in-depth strategies makes these environments a “path of least resistance” for hackers who would rather spend their time on an easy, guaranteed payout than on a difficult, high-stakes attempt against a major corporation.
The political pressure cooker of local governance also plays a central role in the strategic calculation of the attacker. Unlike a private company that can quietly handle a breach behind closed doors, a municipality operates in the public eye. Every service outage is immediately noticed by the citizenry, and the local news media provides a platform for public frustration. This high level of visibility creates a unique form of leverage for extortionists. They know that a mayor or a city manager is under immense pressure to “make the problem go away” as quickly as possible. This pressure is intensified when the outage affects non-negotiable services like water quality monitoring, law enforcement databases, or court proceedings. The threat of a prolonged shutdown of these services is often enough to force a quick settlement, which is exactly what the attackers are counting on when they select a small town as their next target.
Anatomy of a Municipal Cyber Incident: From Infiltration to Detonation
The lifecycle of a municipal cyber incident typically begins not with a sophisticated technical exploit, but with a simple failure of the “human firewall.” Sophisticated phishing campaigns remain the primary entry vector, often involving emails that are meticulously crafted to look like internal communications or legitimate invoices from known vendors. A distracted municipal clerk, balancing the demands of a busy office, might click on a link or open an attachment that appears routine, unknowingly granting an attacker access to the network. These campaigns have become increasingly difficult to detect, as attackers often spend time researching the specific roles and relationships of city employees to make their social engineering attempts as convincing as possible. Once the first set of credentials is stolen, the gate is effectively open.
Another rising threat vector involves third-party risks, where attackers exploit compromised connections from vendors or contractors who have legitimate access to the city’s network. Many small municipalities outsource specialized functions—such as payroll processing, utility billing, or building inspections—to external firms. If one of these vendors has poor security practices, their connection to the municipal network becomes a “backdoor” for hackers. This highlights the reality that a town’s security is only as strong as its weakest partner. Additionally, many small jurisdictions continue to rely on unpatched legacy systems that are no longer supported by their original manufacturers. These “forgotten” servers and old software applications are easy targets for attackers who use automated tools to find and exploit known vulnerabilities that have been left unaddressed due to a lack of technical oversight or budget.
Once inside the network, the attackers enter a “quiet phase” of lateral movement that can last for several weeks. During this period, they navigate the typically “flat” networks of small municipalities, where there is little internal segmentation to prevent an intruder from moving from a low-risk department, like the library, to a high-risk one, like the police department. The primary strategic objective during this phase is the destruction or encryption of backup systems. The attackers understand that if a city has reliable, offline backups, they have no reason to pay the ransom. Therefore, they spend considerable time ensuring that every possible recovery path is blocked before they finally trigger the encryption process. The final “detonation” of the ransomware is the last step in a long and calculated process, leaving the city leadership with the agonizing dilemma of whether to fund a criminal organization or face a recovery process that could take months and cost millions.
The “Pick Three” Framework: Practical Defense for Limited Budgets
Given the severe budget constraints faced by most small municipalities, attempting to implement a comprehensive, enterprise-level security suite is often unrealistic. Instead, a more effective approach is to focus on a “Pick Three” framework that prioritizes the most impactful and cost-efficient defensive measures. The first priority in this framework is the universal implementation of Multi-Factor Authentication (MFA) across all municipal accounts. MFA is widely recognized as the single most effective deterrent against credential-based attacks, as it requires a secondary form of verification that an attacker is unlikely to possess. While there is often organizational resistance to MFA due to the perceived “inconvenience” of the extra step, overcoming this barrier is essential. By making MFA a non-negotiable requirement for every employee, from the mayor to the seasonal parks worker, a municipality can effectively neutralize the majority of phishing attempts.
The second priority involves the establishment of verifiable and isolated backups that are kept separate from the main network. In many recent municipal breaches, the victims discovered too late that their backups were “phantoms”—either they were not running correctly or they had been encrypted by the attackers because they were still connected to the primary network. To defend against this, municipalities must adopt the “3-2-1” backup rule: three copies of the data, on two different types of media, with at least one copy stored entirely offline. Furthermore, these backups must be tested through quarterly restoration drills to ensure that the data is not only present but also usable. Establishing a realistic Recovery Time Objective (RTO) during these tests allows city leaders to understand exactly how long it would take to rebuild their systems from scratch, providing a clearer picture of the risks they face.
The third priority is the proactive establishment of pre-crisis partnerships with state and federal agencies. Many small towns are unaware of the free resources available to them through organizations like the Multi-State Information Sharing and Analysis Center (MS-ISAC). This organization provides 24/7 incident response support, threat intelligence, and vulnerability scanning specifically tailored for local governments. By building these bridges before an incident occurs, municipal leaders ensure that they have an expert “rapid response team” on speed dial when a crisis hits. Additionally, engaging with state-level cybersecurity offices can provide access to grants and shared service agreements that allow small towns to pool their resources with other jurisdictions, creating a collective defense that is far stronger than any individual town could achieve on its own.
Shifting Responsibility: Cybersecurity as an Executive Mandate
The final and perhaps most critical evolution in municipal cybersecurity is the transition of responsibility from the IT department to the executive office. In the past, city managers and department heads could afford to treat digital risk as a technical curiosity that did not require their direct attention. However, in the current threat environment, this attitude is a significant liability. The City Manager must now view themselves as the “Chief Risk Officer” for the community, integrating cybersecurity into every facet of the town’s operations. This means that cybersecurity should no longer be a footnote in the budget but a standing item on the city council agenda. When leadership sets a tone that prioritizes security culture, it cascades through the entire organization, making every employee more vigilant and every department more resilient.
This executive mandate also involves a fundamental change in how vendors and third-party contractors are managed. Every new contract signed by a municipality should include strict cybersecurity requirements, including the right to audit the vendor’s security practices and the requirement for the vendor to notify the city immediately in the event of a breach. By raising the bar for their partners, municipal leaders protect their own networks from the ripple effects of external failures. Moreover, proactive investment in cybersecurity must be framed not as an expense, but as a form of insurance against the catastrophic costs of a reactive recovery. The financial and political toll of a successful ransomware attack is almost always many times higher than the cost of implementing basic defenses like MFA and isolated backups.
As communities looked toward the future of their digital infrastructure, the realization dawned that the era of “security through obscurity” had officially ended. The small towns that successfully navigated this transition were those where the leadership recognized that protecting the community’s data was just as vital as protecting its physical property. By moving beyond the outdated notion that they were too small to be targeted, these municipalities began to build a culture of resilience that prioritized the continuity of essential services above all else. The long-term value of this proactive stance was measured not only in the avoidance of ransom demands but in the preservation of public trust. When the executive leadership took ownership of the digital defense, they transformed cybersecurity from a source of fear into a manageable component of modern governance, ensuring that the essential functions of the community remained secure against an ever-evolving threat.