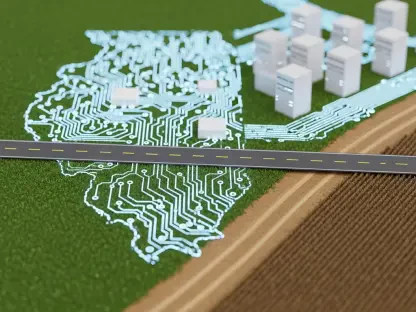
The digital silent war has moved from the encrypted servers of Washington D.C. to the unassuming water valves and school district databases of rural America, where a single keystroke can now disrupt the lives of thousands. While national headlines often focus on high-level federal breaches, a more insidious threat is targeting the local water systems, school districts, and municipal utilities that form the backbone of American daily life. These local entities, frequently operating on shoestring budgets and aging hardware, have become the soft underbelly of the nation’s defensive posture. The central question facing civic leaders is whether a small-town budget can truly withstand a state-sponsored cyberattack specifically designed to cripple public infrastructure. Current data suggests that the answer is a resounding no, as nearly 68% of state, local, tribal, and territorial governments report they lack the necessary funding to address their most critical security priorities. This financial and operational gap has transformed local agencies into the new front line of national defense, necessitating a rapid shift toward a unified, “whole-of-state” security model.
This systemic vulnerability is not merely a technical glitch but a strategic crisis that requires a fundamental reimagining of how local governments interact with federal security standards. The “whole-of-state” approach seeks to break down the walls between different levels of government, allowing for shared intelligence, pooled resources, and a synchronized response to threats that do not respect municipal boundaries. By viewing cybersecurity as a collective responsibility rather than an individual burden, local agencies can leverage the weight of federal expertise and state-level coordination to fortify their perimeters. This transition is essential because the cost of failure at the local level—ranging from contaminated water supplies to the exposure of millions of citizens’ personal records—is far too high for the nation to ignore.
The Hidden Vulnerability of the Local Utility Grid
The modern utility grid is a complex tapestry of interconnected systems where the distinction between physical infrastructure and digital code has almost entirely vanished. In many jurisdictions, the same software that manages billing and administrative tasks is tethered to the physical pumps and switches that regulate essential services like electricity and clean water. This convergence has created a situation where a compromise in a municipal office can have immediate, tangible consequences in the physical world. For a hacker, the path of least resistance is no longer a hardened federal database but a local utility that may still be relying on default passwords or unpatched software from the last decade.
Addressing this vulnerability requires a move away from isolated security “islands” and toward a more integrated ecosystem. When a local government adopts a “whole-of-state” model, it gains access to advanced monitoring capabilities that would be otherwise unaffordable. This model allows for the implementation of centralized security operations centers that can monitor dozens of smaller municipalities simultaneously, providing a level of oversight that mimics federal-grade protection. Without this shift, local agencies will remain trapped in a cycle of reactive patching, always one step behind adversaries who possess the time, talent, and technology to exploit even the smallest oversight.
Bridging the Resource Gap in a Volatile Threat Landscape
The divide between the sophistication of modern cyber threats and the legacy resources available to local governments has reached a breaking point. Foreign adversaries have pivoted from targeting federal systems to exploiting the fragmented defenses of sub-federal entities, where legacy silos often prevent a cohesive response. These adversaries recognize that local governments are the custodians of vast amounts of sensitive data and the operators of critical life-support systems, yet they are often the least equipped to defend them. To counter this, state and local leaders are increasingly looking toward the White House’s “Cyber Strategy for America” as a blueprint for survival.
This strategy serves as more than just a list of recommendations; it is a framework for fundamental structural change. By aligning local operations with federal pillars, agencies can move away from “stitching together” disconnected security tools and instead build a modernized foundation that prioritizes efficiency and shared visibility. This alignment is particularly crucial for agencies that have historically struggled with “technical debt”—the accumulated cost of maintaining outdated systems rather than investing in new ones. By adopting a unified strategy, these agencies can justify the transition to modern platforms that offer better protection at a lower long-term operational cost.
Moreover, the shift toward a unified strategy fosters a culture of proactive defense. Instead of waiting for an incident to occur and then scrambling to find the resources for a recovery, local leaders can implement standardized security protocols that are recognized across all levels of government. This standardization makes it easier for different agencies to collaborate during a crisis, ensuring that the response is fast, coordinated, and effective. The goal is to create a seamless defensive web where a threat detected in one county is immediately flagged and blocked in every other jurisdiction across the state.
Implementing the Pillars of Critical Infrastructure and Emerging Tech
The national strategy provides a clear roadmap for hardening the essential services that citizens rely on every day. Pillar Four emphasizes the protection of critical infrastructure through the convergence of Information Technology (IT) and Operational Technology (OT), ensuring that an attack on a corporate network cannot easily jump to physical utility control systems. In the past, these two domains were often managed by entirely different departments with little communication between them. Today, the strategy mandates that they be viewed as a single, integrated environment where security is baked into every connection, from the office desktop to the industrial sensor.
Simultaneously, Pillar Five highlights the necessity of “machine speed” defense to keep pace with automated threats. For state and local agencies, this means establishing an AI-ready data foundation that breaks down departmental silos and centralizes information for rapid analysis. By centralizing data access, governments can deploy automated threat detection and natural-language queries, allowing resource-constrained teams to manage complex logs without the manual labor typically associated with legacy systems. This allows a small team of IT professionals to perform the work of a much larger department, identifying patterns and anomalies that would be impossible for a human to spot in real-time.
Furthermore, an AI-ready foundation provides the necessary guardrails to manage the risks of emerging technologies. As local employees begin to explore the use of artificial intelligence in their daily workflows, the risk of “Shadow AI”—where unmanaged tools are used outside of official oversight—grows significantly. A modernized infrastructure allows for the implementation of governed AI environments, ensuring that the benefits of automation are realized without compromising the security or privacy of citizen data. This proactive stance on technology adoption is a key component of the national strategy’s vision for a resilient digital future.
Quantifying the Impact of AI-Driven Security Operations
The urgency of this transition is supported by alarming trends, including FBI data showing a 50% increase in ransomware complaints from critical infrastructure organizations over a two-year period. This surge is not a random occurrence but a calculated effort by criminal enterprises and state actors to extort money and sow chaos at the local level. Expert consensus indicates that the only viable path forward is the adoption of AI-driven Security Information and Event Management (SIEM) platforms. These platforms serve as the central nervous system of a modern security operation, collecting and analyzing data from every corner of the network to provide a real-time picture of the threat landscape.
These tools do more than just speed up response times; they mitigate the risks of unmanaged consumer tools and drastically reduce alert fatigue by filtering out false positives. In a traditional security environment, analysts are often overwhelmed by thousands of alerts, most of which are harmless background noise. AI-driven systems use machine learning to prioritize high-profile threats, allowing human analysts to focus their energy on the most critical vulnerabilities. By utilizing Large Language Models (LLMs) to provide context and natural-language explanations of complex events, even junior analysts can make informed decisions during a crisis.
This efficiency is not just a technical luxury; it is a financial necessity in an era of chronic budget shortages. When a system can automatically identify and neutralize a threat before it causes damage, the potential savings in terms of incident response and recovery costs are astronomical. For many local governments, the investment in an AI-driven SIEM platform pays for itself the first time a major ransomware attack is thwarted. By shifting the focus from administrative maintenance to active defense, agencies can maximize the impact of their limited resources and provide a higher level of safety for their constituents.
A Practical Framework for Scaling Modernized Defenses
Turning national strategy into local reality requires a focus on interoperability and proven success models, such as the transformation seen within California’s Employment Development Department (EDD). Tasked with managing a staggering volume of data, the agency successfully secured 850 billion records across 14,000 endpoints by adopting an AI-powered SIEM platform. The most impressive result was a 99% reduction in the mean time to respond (MTTR) to cyber events, a feat that would have been impossible using legacy methods. This case study demonstrates that even the largest and most complex state agencies can achieve rapid modernization when they prioritize the right tools and strategies.
To replicate these results, local leaders should prioritize open standards that allow for integration across cloud and on-premises environments without incurring runaway licensing costs. The goal should be a flexible architecture that can grow and adapt as the threat landscape changes, rather than a rigid system that becomes obsolete within a few years. Implementing tiered data storage and consolidating redundant tools provides a sustainable financial path for agencies to meet compliance mandates while maintaining a proactive, data-driven security posture. By focusing on consolidation and efficiency, agencies can free up the funds necessary to invest in the next generation of defensive technologies.
The path forward for state and local governments involved a deliberate commitment to the principles of the National Cyber Strategy. Leaders recognized that the traditional, fragmented approach to security was no longer sufficient to protect the essential services of a digital society. By embracing AI-driven operations and a “whole-of-state” mindset, these agencies shifted the balance of power back in favor of the defenders. They successfully transformed their legacy infrastructures into resilient, data-centric environments capable of weathering the most sophisticated attacks. This proactive alignment ultimately ensured that the local utilities, schools, and services that citizens depend on remained secure, demonstrating that even the smallest municipality can be a vital link in the chain of national defense. Through these actionable steps, the vision of a unified and secure digital infrastructure became a tangible reality for communities across the country.